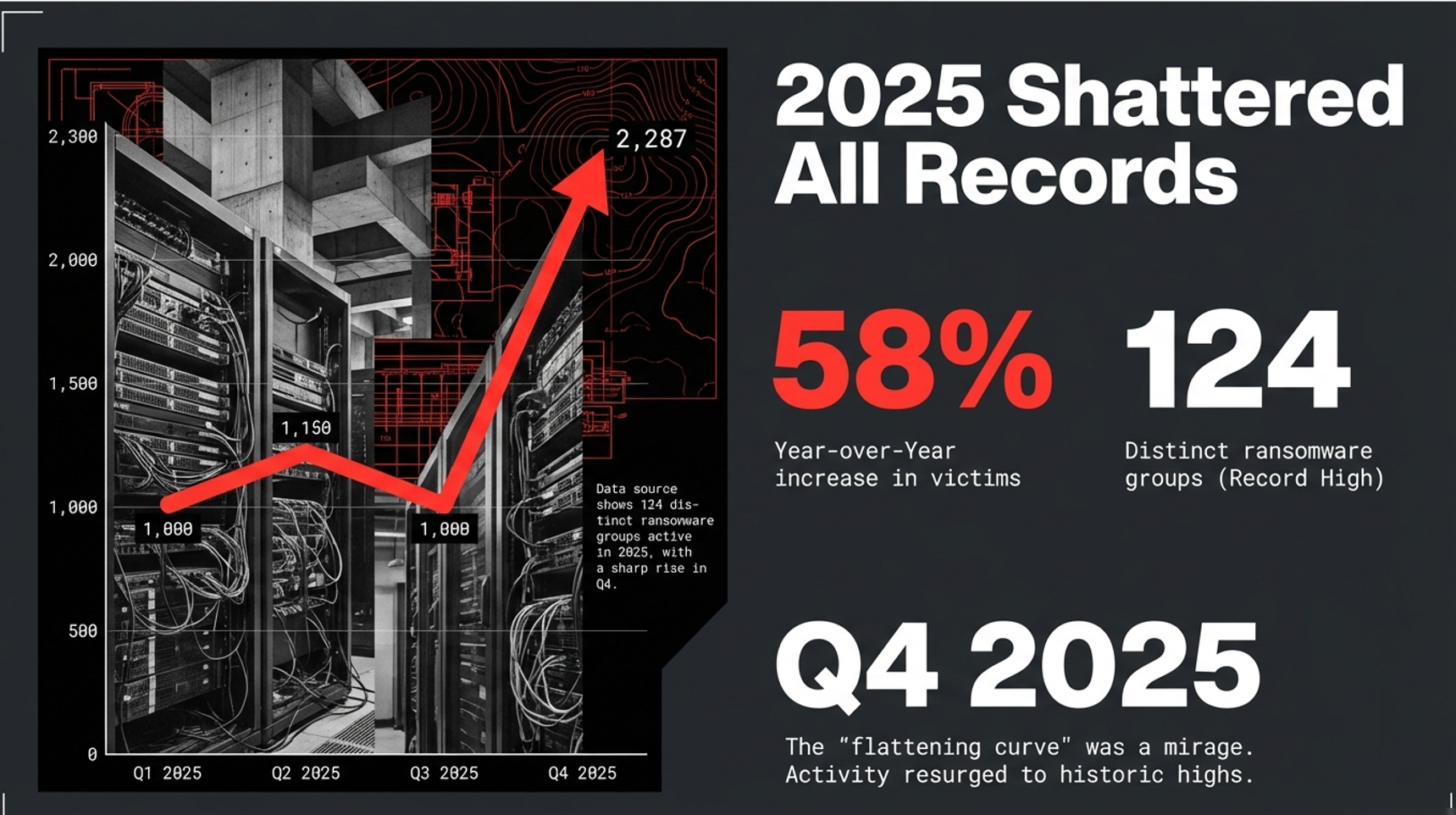
2026 MSP Security Strategy: Industrialized Threats and the New MSP Reality
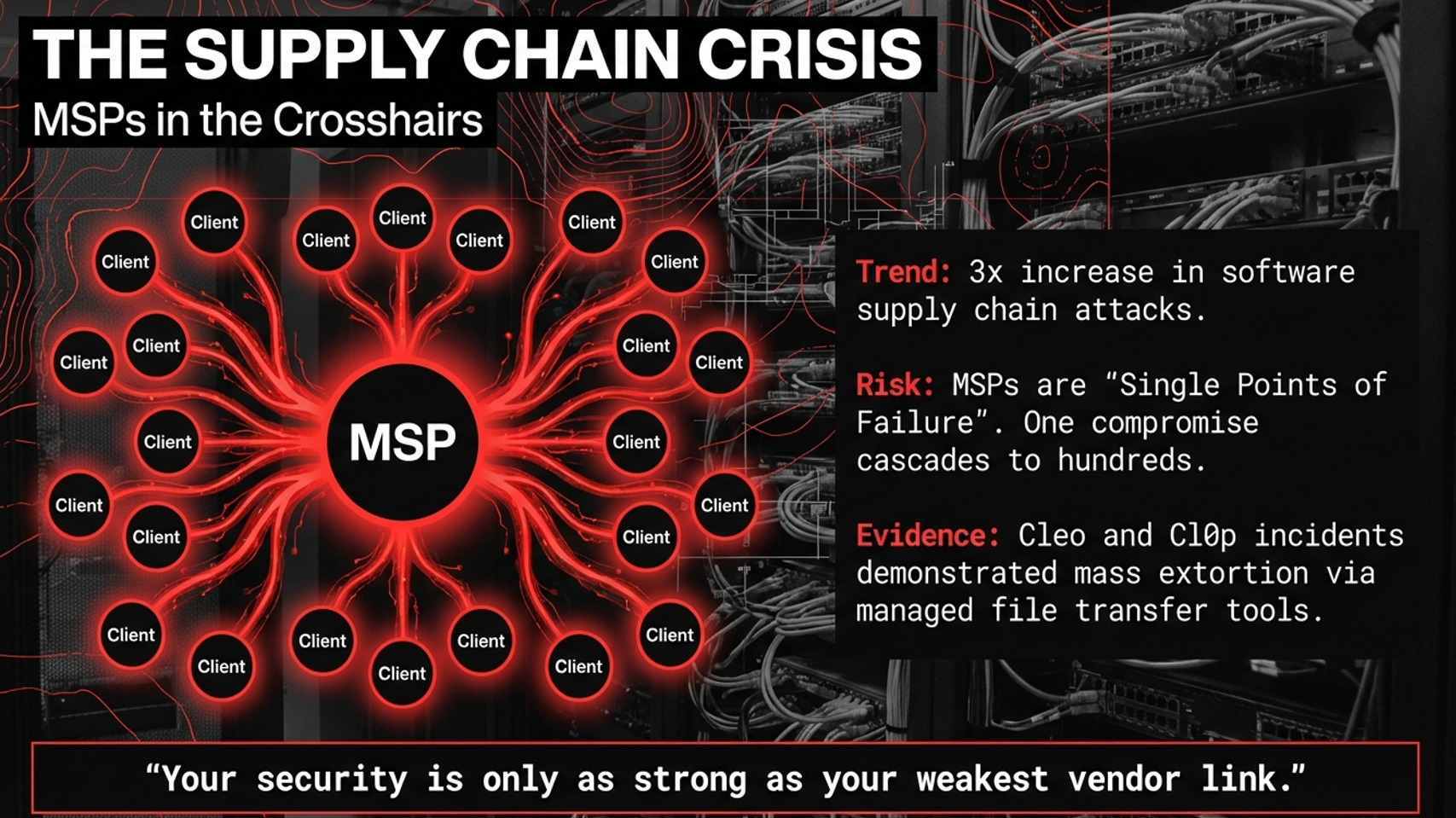
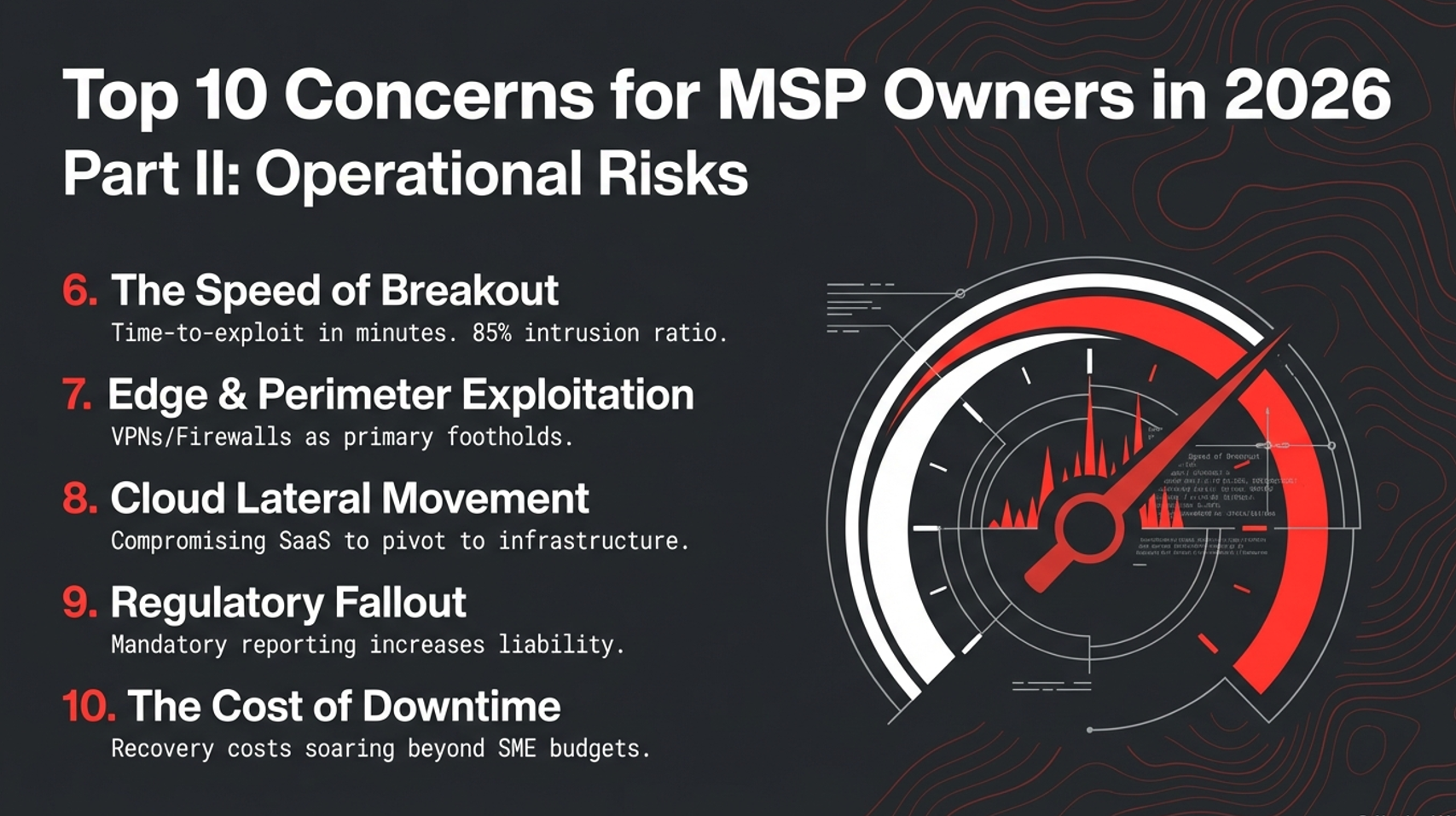
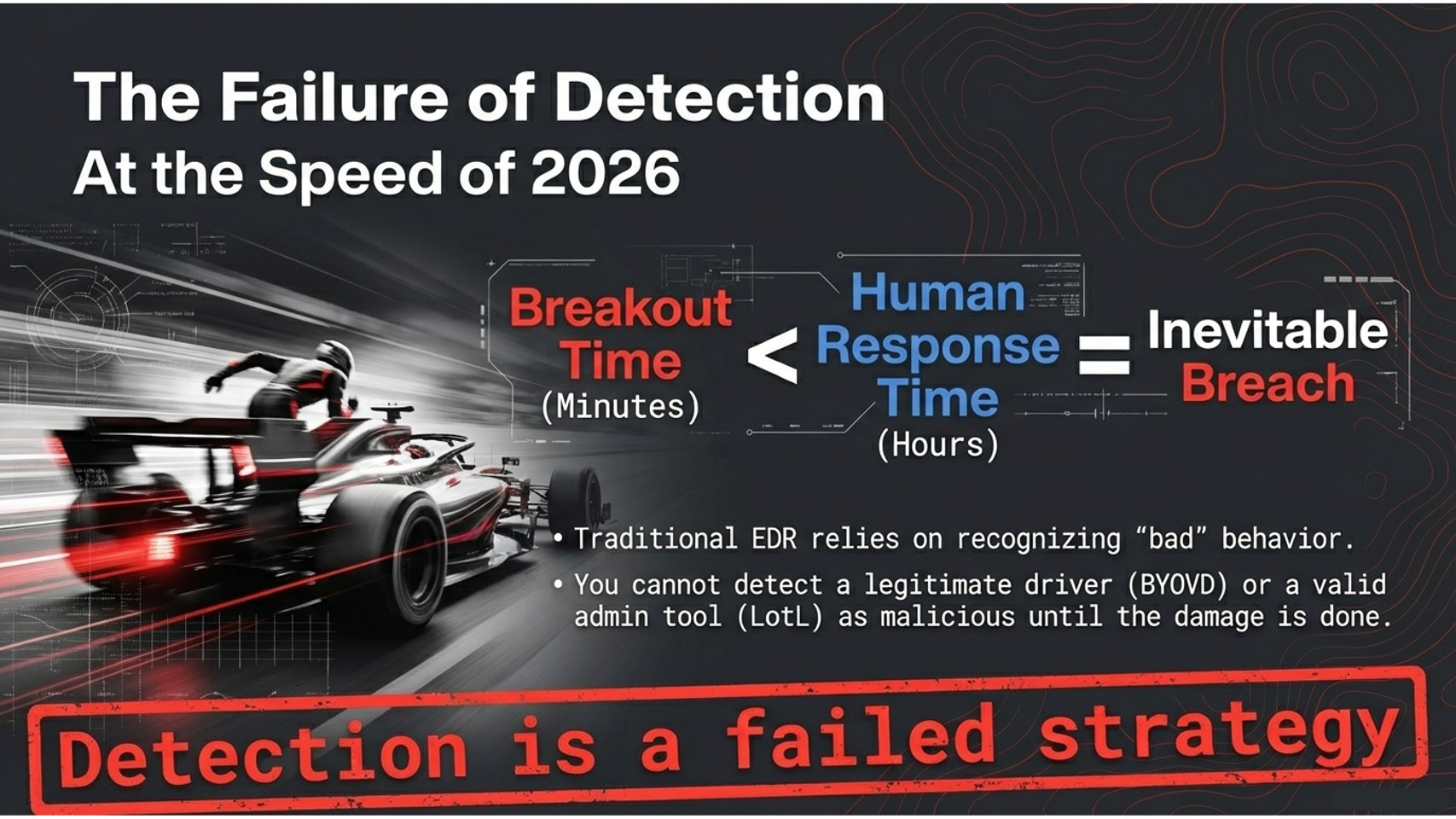
2026 is shaping up to be a pressure test for MSP owners: faster breakout timelines, identity-first intrusions, supply-chain exposure, and more client endpoints stuck in “forever-day” conditions as legacy operating systems age out of support. If your security stack depends on catching bad files or responding to alerts in time, you’re fighting a timing problem, not a tooling problem.
What changed and why MSPs feel it first
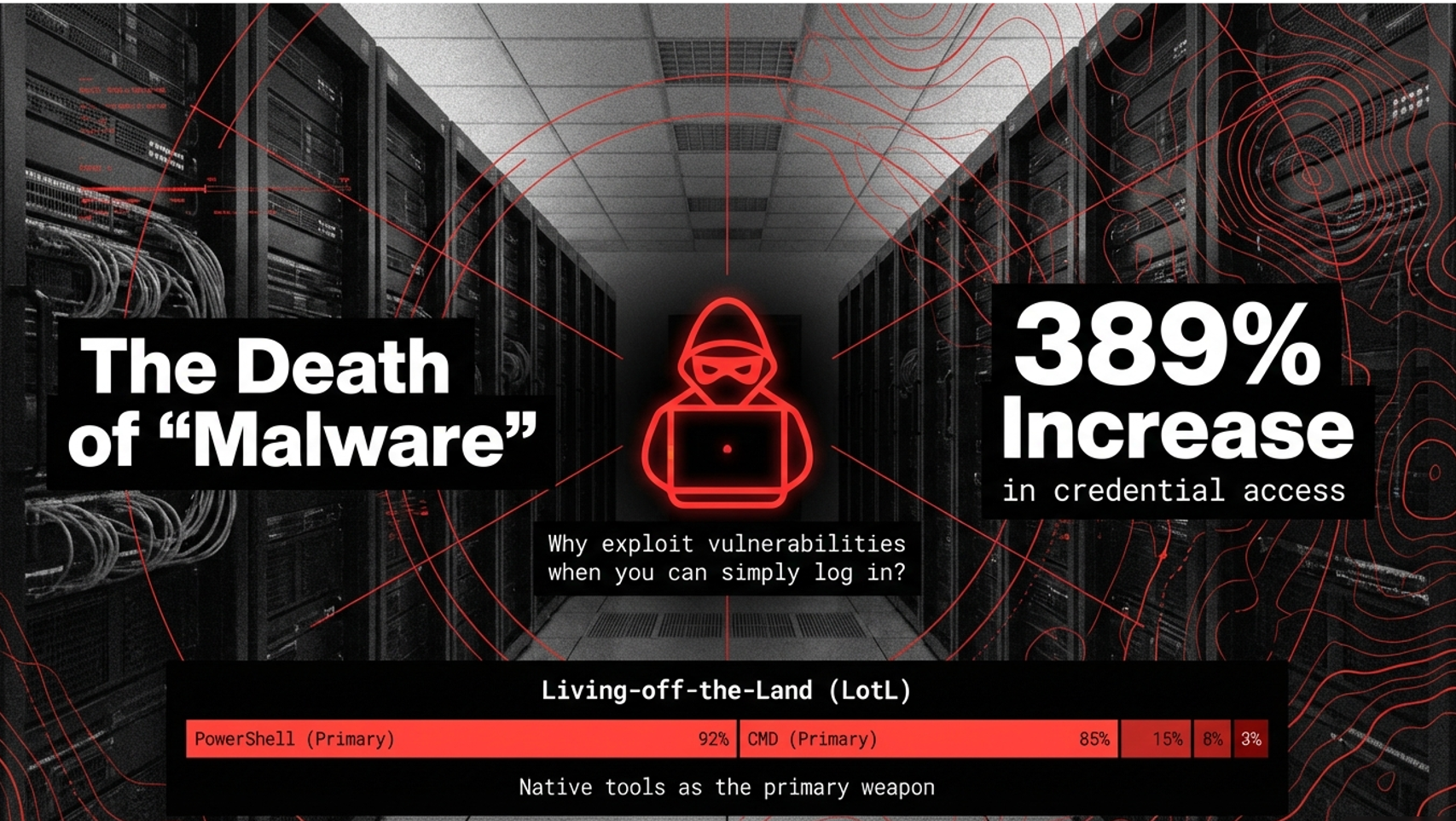
Threat actors increasingly avoid “classic malware” and instead use valid credentials, built-in administrative tools, and trusted processes. That makes detection noisy and inconsistent and turns your MSP into the blast radius when a single tool or tenant is compromised.
The 2026 risk pattern MSP owners should plan for
- Identity abuse: attackers log in instead of breaking in.
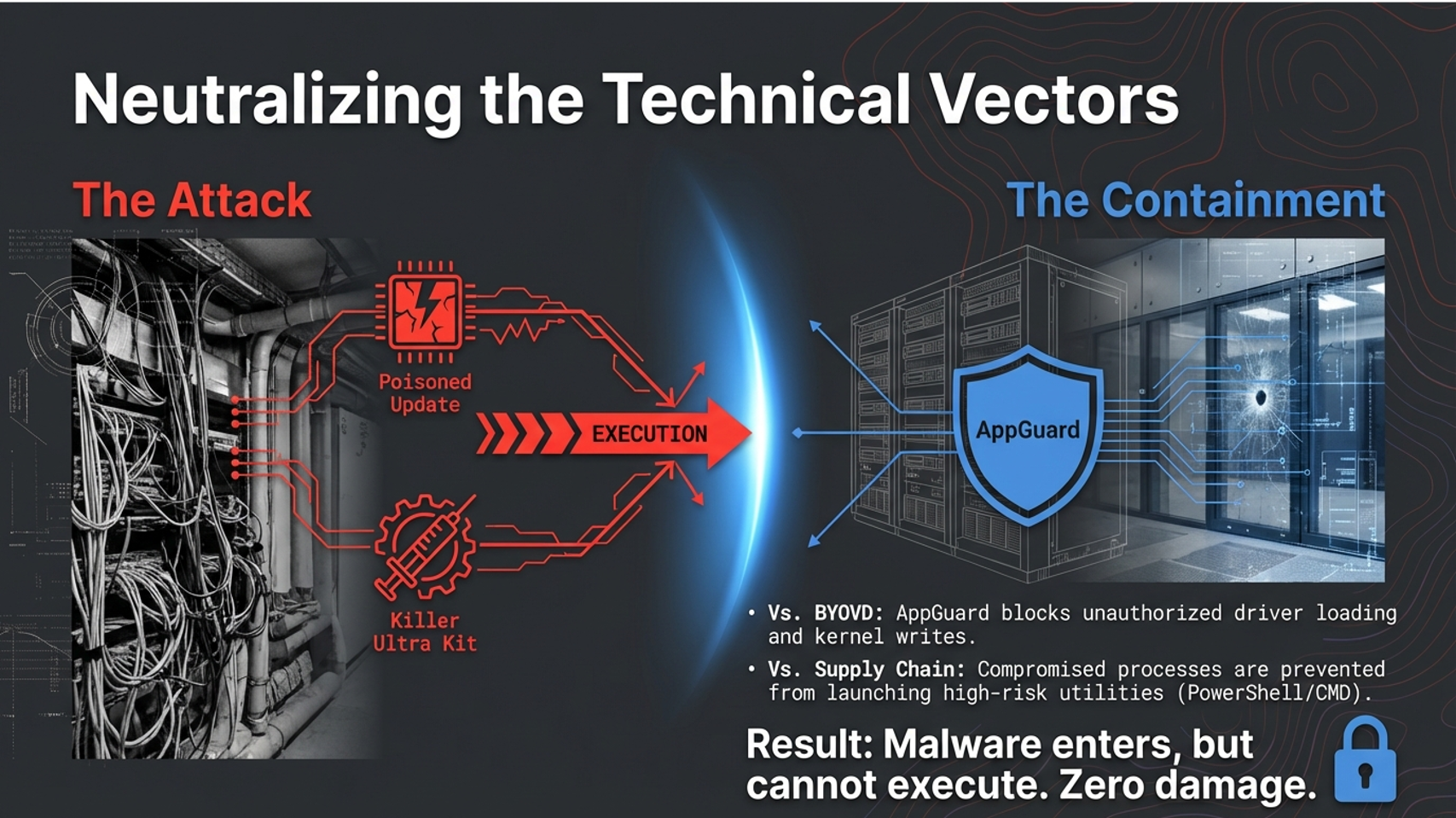
- Supply-chain exposure: trusted tools and updates become delivery paths.
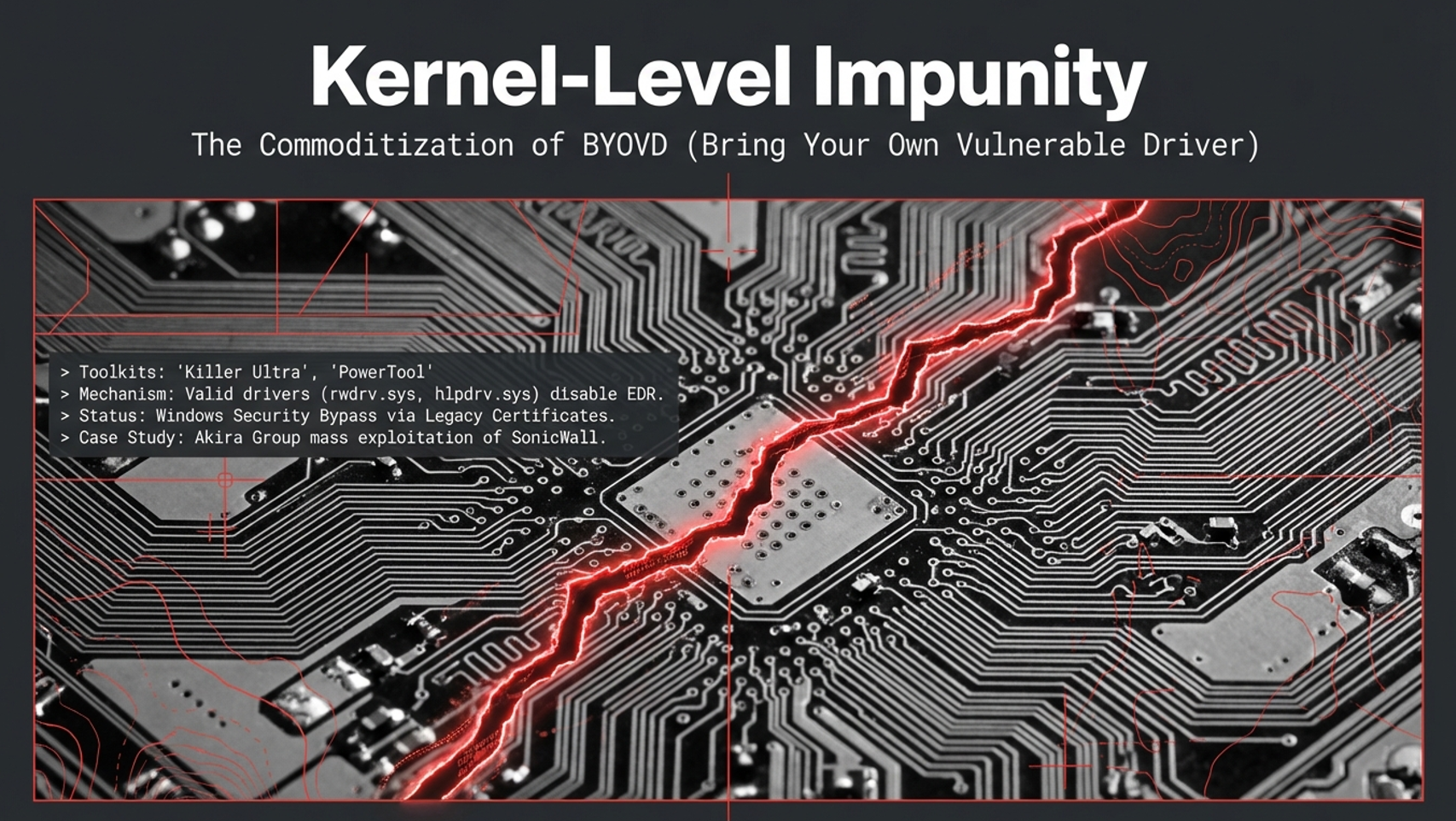
- Kernel-level tactics: vulnerable drivers and kill-chains designed to disable protections.
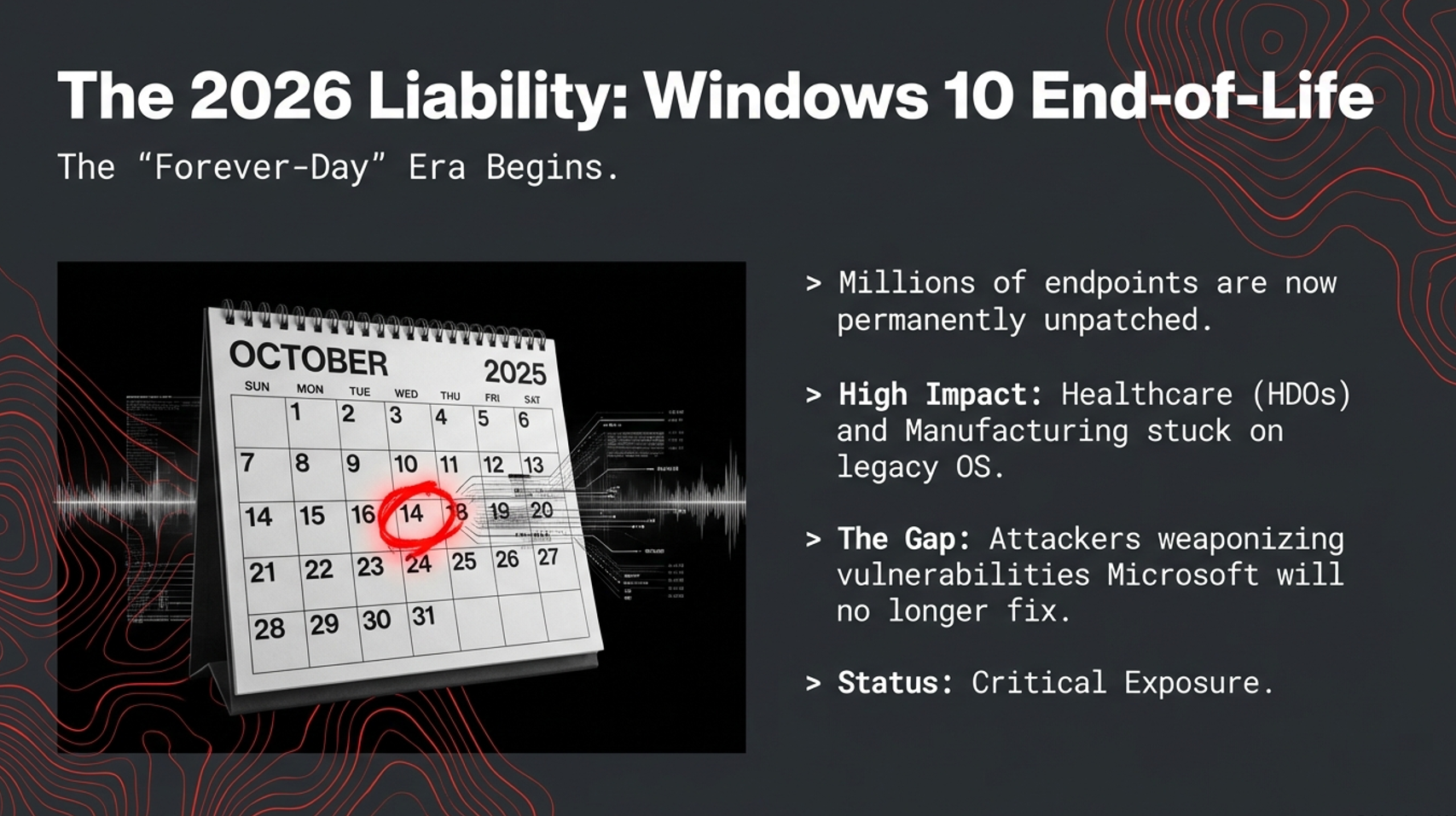
- Legacy endpoints: more environments operate with limited patch options and higher exposure.
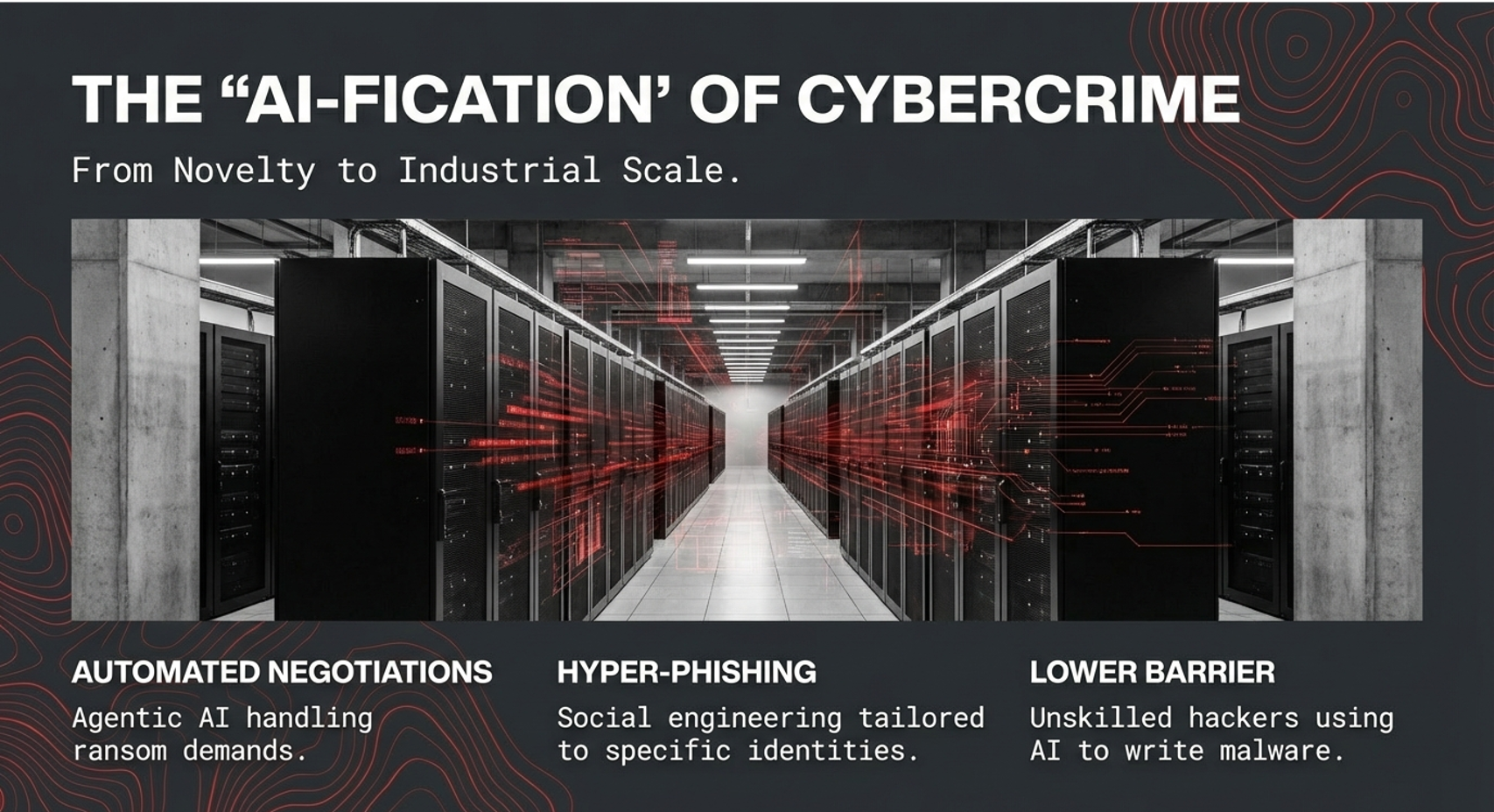
- Automation: AI-enabled crime lowers the barrier and speeds execution.
What to do differently: containment over chasing alerts
A prevention-first approach focuses on blocking harmful actions and containing abuse paths even when the process looks “legitimate.” For MSP owners, the business outcome is simple: fewer escalations, less security noise, lower client disruption, and more predictable margins.
Next steps: review the Top 5 Business Reasons, explore FAQ, or Get Started.